Take advantage of the digital transformation
The sudden change in social behaviors and work methodologies has led to the emergence of new needs that even the big digital giants have often found themselves unprepared for. If you are able to make your business processes more efficient and capture the attention of your customers, you will inevitably see a marked increase in profits and a modern, competitive business strategy that is one step ahead of the competition.

END to END IT services
End-to-end solutions offer comprehensive systems that keep pace with a business’s ever-changing infrastructure requirements, and the changing demands of the IT sector itself. This might cover everything from the client interface to data storage and generally handle all of a system's hardware and software, including installation, implementation, and maintenance.

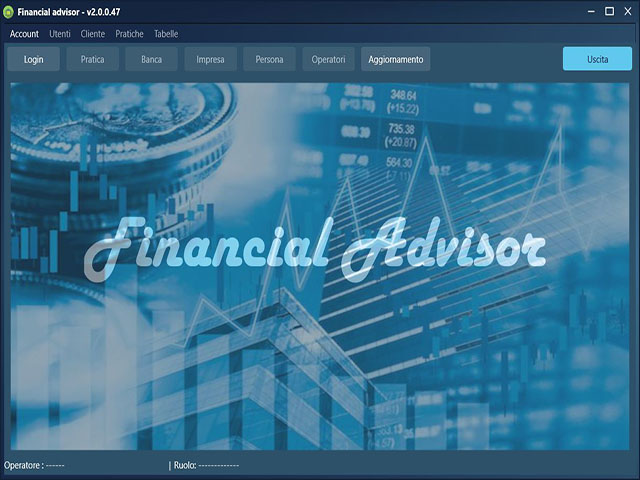
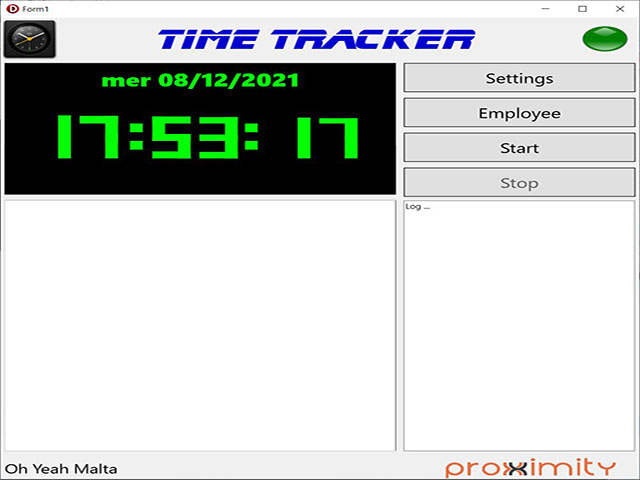
Custom development
Every company needs a software to run their business. In many cases they can use generic applications designed for the industry, but it can happen, that those software do not completely fit their needs. Whatever is your way of working, Proxximity can build custom software to run part or all of your business giving the company a great "value" asset.

WEB development
Having a solid web presence today is an essential component of your marketing strategy. It doesn't matter how big your business is or what industry you're in. Being online strengthens your brand and increases the value of what you offer to your target audience. It helps your potential customers find the products and services you sell, spreads awareness and knowledge of your brand.

Mobile and IoT development
Mobile development is not only building phone apps. In fact, this type of development encompases developing apps for phones, tablets, smart watches, and all other kinds of wearable devices which run some kind of mobile operating system, including IoT (Internet of things).

Modernize legacy software
Legacy application modernization is the process of replacing an outdated software product with a modern one, using the latest technology trends and the most appropriate stack to update an old design. This solution is often better, than adding new features in the legacy code turning complex systems into sophisticated ones.

Blockchain
In order to exploit the full potential of Blockchain Technology, Proxximity has started to develop decentralized platforms using smart contracts, reducing the risks of downtime, censorship, fraud or third party interference. Application areas vary between Authentication & Authorization, Digital Content, Kyc/Aml, Supply Chain, etc..